1. Run Hydra MTK Tool.
2. Choose Brand and Module.
3. Go "Service"-->"Tooll"
4. Choose "Factory Reset Protection FRP" from universal menu..
5. Choose "Format / Erase" from drop down "Method / Option"
6. Click "Execute"
7. Connect cellphone to computer with the help of USB Data Cable.
8. Wait until the operation is completed.
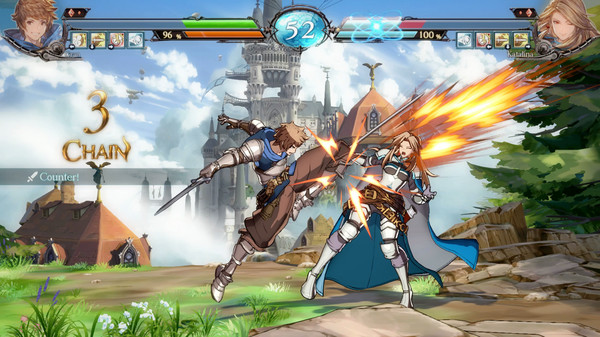
Screen Short:

Logs:
|
===================================== Searching for MTK Device...Found Port Identification :Flashmode Preloader FriendlyName :MediaTek PreLoader USB VCOM_V1632 (Android) (COM15) Device :5&212ac8fc&0&1 SymbolicName :\??\USB#VID_0E8D&PID_2000#5&212ac8fc&0&1#{a5dcbf1 0-6530-11d2-901f-00c04fb951ed} Driver Ver :01/22/2015,3.0.1504.0 Handshaking...Ok Identifying Hardware ID..... Reading Device hardware info.. hw code : 0766MT6765 [6765] hw subcode : 8A00 hw version : CA00 sw version : 0000 Target config : 05 SB : 01 (True) SLA : 00 (False) DAA : 04 (True) FUSEID : 00000000 SECURE VERSION : 00 BL VERSION : 03 NORMAL BOOT Preparing Download Agent.. DA : 6765_SWSEC_9FAA6CBA20.bin Agent: MTK_DOWNLOAD_AGENT -HYDRA Ver : MTK_AllInOne_DA_v3.3001.2018/03/20.21:08_402229+403250 Init : Loader [1] Sending : Accepted Identifying Protocol... Protocol : New Synchronization...SYNC Mode : preloader Execute Secondary Loader Init : Loader [2] Executing : SYNC Reading Device UniqueID, RAM and Flash Chip Info... UNIQUE ID : E4A9830703DAAB3435AF90F9B6009074 ERAM Size : 0x0000000000040000 -256 KB IRAM Size : 0x0000000020000000 -512 MB eMMC BOOT1 : 0x0000000000400000 -4 MB eMMC BOOT2 : 0x0000000000400000 -4 MB eMMC RPMB : 0x0000000001000000 -16 MB eMMC USER : 0x0000000747C00000 -29.121 GB eMMC CID : 150100514436334D4201D38607DC1775 - QD63MB DA Speed : high-speed Reading GPT-EMMC [0x00008000] 130 Items Reading System Info Brand : vivo Vendor : vivo Model : vivo 1820 ID : O11019 SDK : 27 Release : 8.1.0 ABI : arm64-v8a CPU abilist : arm64-v8a,armeabi-v7a,armeabi Locale : en-US Description : full_k62v1_64_bsp-user 8.1.0 O11019 1598442376 release-keys Device : PD1818HF_EX Display ID : O11019 release-keys Security Patch : 2020-08-01 Platform : =MTK6765 Fingerprint : vivo/1820/1820:8.1.0/O11019/1598442376:user/release-keys StorageType : mtp Userdata State : Encrypted Autobackup Partitions -preloader[0x00000000]512 KB ->preloader.bin...Ok -> Renaming Preloader.... preloader_k62v1_64_bsp.bin Creating Scatter file... C:\Hydra Tool\\Backup\Auto\0766_vivo_1820_1820_8.1.0_O11019 _1598442376_053121155328\MT6765_Android_scatter.tx t -pgpt[0x00000000]32 KB ->pgpt.bin...Ok -frp[0x05588000]1024 KB ->frp.bin...Ok -nvdata[0x07688000]64 MB ->nvdata.bin...Ok -protect1[0x16A88000]8 MB ->protect1.bin...Ok -protect2[0x17288000]13.469 MB ->protect2.bin...Ok -persist[0x18800000]48 MB ->persist.bin...Ok -nvram[0x25680000]64 MB ->nvram.bin...Ok Done!!! C:\Hydra Tool\\Backup\Auto\0766_vivo_1820_1820_8.1.0_O11019 _1598442376_053121155328 MTK Phone Loader is NOW RUNNING. Reading Device UniqueID, RAM and Flash Chip Info... UNIQUE ID : E4A9830703DAAB3435AF90F9B6009074 ERAM Size : 0x0000000000040000 -256 KB IRAM Size : 0x0000000020000000 -512 MB eMMC BOOT1 : 0x0000000000400000 -4 MB eMMC BOOT2 : 0x0000000000400000 -4 MB eMMC RPMB : 0x0000000001000000 -16 MB eMMC USER : 0x0000000747C00000 -29.121 GB eMMC CID : 150100514436334D4201D38607DC1775 - QD63MB Reading GPT-EMMC [0x00008000] 130 Items Reading System Info Brand : vivo Vendor : vivo Model : vivo 1820 ID : O11019 SDK : 27 Release : 8.1.0 ABI : arm64-v8a CPU abilist : arm64-v8a,armeabi-v7a,armeabi Locale : en-US Description : full_k62v1_64_bsp-user 8.1.0 O11019 1598442376 release-keys Device : PD1818HF_EX Display ID : O11019 release-keys Security Patch : 2020-08-01 Platform : =MTK6765 Fingerprint : vivo/1820/1820:8.1.0/O11019/1598442376:user/release-keys StorageType : mtp Userdata State : Encrypted ------------------------------------- Operation : Format/Erase Processing... Erasing FRP Partition... Ok Rebooting Device [Reboot To Normal] Reboot Done!! Elapsed Time : 00:00:36 |
Dipendra Pathak
by Dipendra Pathak via GSM-Forum